Sophos Network Detection and Response
Sophos NDR Provides Critical Visibility into Network Activity That Other Products Miss
Detect Suspicious Behaviors That Extend Beyond Your Firewalls and Endpoints
.png?width=530&quality=80&format=auto&cache=true&immutable=true&cache-control=max-age%3D31536000)
Sophos NDR detects a range of network behaviors, making it an effective solution for identifying:

Unprotected Devices
Identify legitimate devices that aren't protected and could be used as entry points, including IoT and OT assets.

Rogue Assets
Pinpoint unauthorized and potentially malicious devices communicating across a network.

Insider Threats
Gain visibility to network traffic flows and “normal” data movement from inside an organization.

Zero-Day Attacks
Detect server command-and-control (C2) attempts based on patterns found in session packets.
Early Detection and Automatic Response
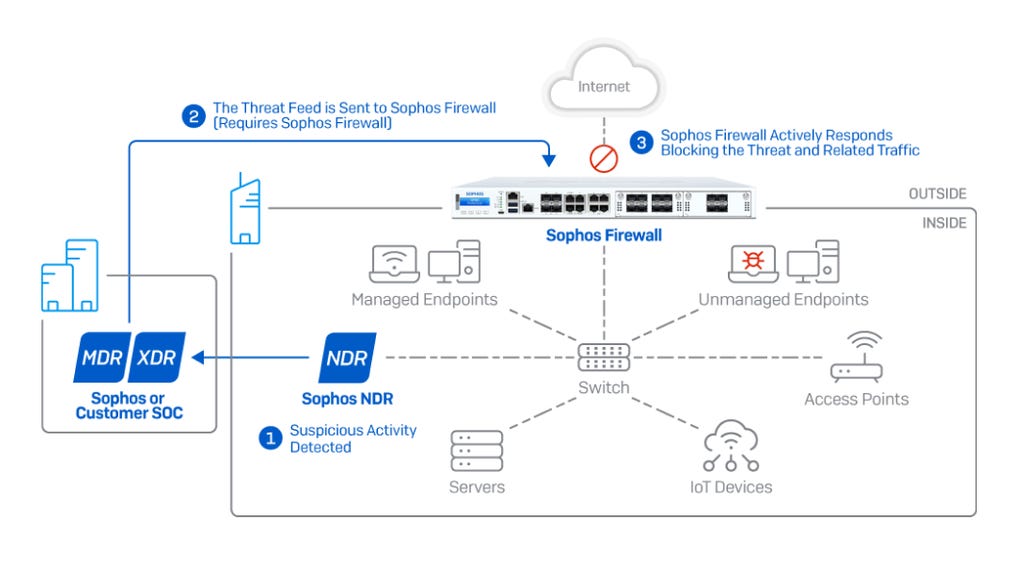

How it works: Sophos NDR monitors traffic deep within the network, sending suspicious activity to Sophos Central’s data lake for further analysis. In the event an active threat or adversary is identified, analysts can immediately push a threat feed to Sophos Firewall that can coordinate an Active Threat Response to isolate and block malicious activity automatically in real-time.
5 Independent Detection Engines That Work in Real-Time
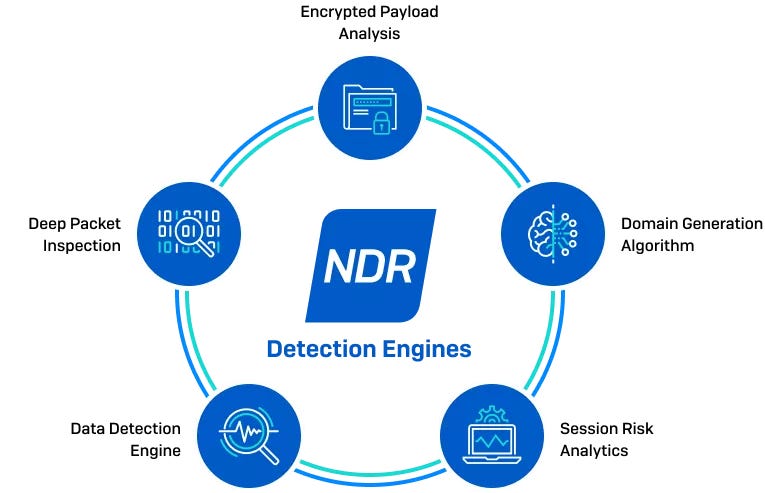
Data Detection Engine
Domain Generation Algorithm
Identifies dynamic domain generation technology used by malware to avoid detection.
Deep Packet Inspection
Session Risk Analytics
Powerful logic engine utilizes rules that send alerts based on session-based risk factors.
Encrypted Payload Analysis
Get valuable insights and perform deep investigations
Sophos Central and the Sophos NDR Investigation Console provides all the tools you need to easily:
- Get instant insights into into network and application activity, risky flows, and suspicious traffic detections in Sophos Central
- Drill-down and perform deep forensic investigations with the Investigation Console
- Identify all unmanaged, IoT, and potential rogue assets on your network including their manufacturer and operating system
Frequently asked questions
Network Detection and Response (NDR) gives you clear visibility into what is happening across your network. It continuously monitors network traffic and flags suspicious or malicious activity, including threats that can slip past endpoints or perimeter controls. NDR passively inspects traffic using five detection engines (with some analytics running on a schedule for deeper correlation) and sends actionable detections into Sophos Central so your team can investigate and respond quickly.
NDR reveals what is happening inside your network (east-west traffic) as well as traffic entering or leaving it (north-south traffic). This level of visibility helps you detect suspicious activity between devices, command-and-control (C2) behavior, and unusual data movement. It strengthens your defenses across the entire attack surface, not only at the perimeter.
Each tool plays a different role:
- EDR monitors activity on endpoints.
- NDR analyzes network traffic to expose suspicious activity between devices, including unmanaged, internet-of-things (IoT), and rogue devices.
- SIEM collects and correlates log data.
- Firewalls manage and control traffic entering and leaving the network.
Sophos NDR complements these tools by adding AI-powered network analytics and delivering high-value detections directly into Sophos Central to support extended detection and response (XDR) and managed detection and response (MDR) workflows.
Some threats hide in network behavior rather than leaving clear traces on endpoints. NDR helps uncover activity such as lateral movement, malware command-and-control (including zero-day C2 patterns), rogue or unmanaged devices, insider-driven data movement, and suspicious encrypted traffic behavior. By focusing on network activity, NDR brings these blind spots into view.
NDR blends deep learning, behavioral analytics, and rule-based logic across multiple detection engines. It correlates evidence and applies clustering and scoring before generating detections. This approach cuts down on noise, improves accuracy, and helps identify unknown or encrypted threats without overwhelming the team.
NDR analyzes network flows created from packet data and enriches them with protocol details, traffic behavior, TLS attributes, and other risk indicators. Deployment is simple: A passive sensor connects to a SPAN or mirror port, providing broad visibility without adding latency, disrupting operations, or introducing an inline point of failure.
NDR is flexible. You can deploy it as a virtual appliance on VMware or Hyper-V, run it in AWS, or use certified hardware. Sensors monitor important network segments, and detections flow into Sophos Central for a unified view across on-premises and cloud environments.
NDR detections feed into Sophos Central, where analysts can investigate, correlate telemetry, and act. Integrated workflows can also push threat intelligence to other Sophos products. For example, analysts can push a threat feed to Sophos Firewall to trigger Active Threat Response, automatically isolating a compromised host and blocking related malicious communications to contain threats faster.
A strong NDR solution should offer multiple detection techniques, AI-based encrypted traffic analysis, high-value detections supported by scoring, flexible deployment choices, and smooth integration with XDR or MDR programs. The right solution should close visibility gaps and improve response times without adding operational complexity.
Sophos NDR is licensed based on users and servers, with the virtual appliance included in the subscription. Organizations justify ROI by closing visibility gaps, reducing dwell time, improving analyst efficiency with high-value detections, and speeding containment through automated response workflows, helping prevent costly incidents while increasing the impact of existing security investments.
.svg?width=185&quality=80&format=auto&cache=true&immutable=true&cache-control=max-age%3D31536000)


.svg?width=13&quality=80&format=auto&cache=true&immutable=true&cache-control=max-age%3D31536000)

